The statement that the "annual cost of around $200 (£150) per employee associated with using passwords" is given out of context.
It isn't the use of passwords themselves that cost that much, it's the cost of what happens after passwords are compromised and the accounts are broken into.
The article says:
Facebook admitted in April that the passwords of millions of Instagram users had been stored on their systems in a readable format
This practice is inexcusable.
There is no need for any organization or software to store passwords in any format whatsoever.
Operating systems such as UNIX have known this for over 40 years, and simply do not store passwords.
Instead they use the entered password as the key for encrypting something else, and they store that encrypted value.
The password itself exists only in temporary memory and never appears in any file.
Other than brute force guessing, it's impossible for anyone, even the owners of the data, to determine the original password from the encrypted value.
The article also says:
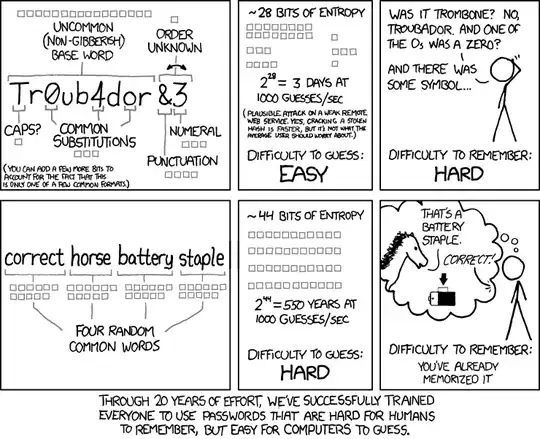
People tend to use passwords that are easy to remember and therefore easy to compromise.
The cause of the problem is systems that go to the extremes of allowing trivial passwords or enforcing complicated rules that force people to write down their passwords.
This again is totally avoidable.
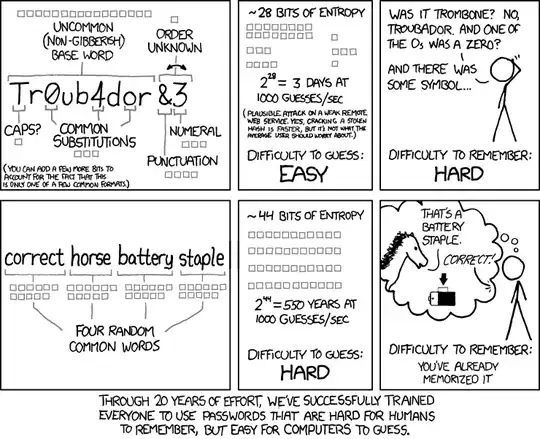
Microsoft's Windows 10 system for example requires a mixture of digits, upper and lower case, and special characters.
The result is of course very difficult to remember, and often ends up on a piece of paper under the keyboard.
They do offer a solution though: if one can't remember the password, a secret 4-digit emergency PIN can be used instead.
(Read that last statement again and think about it.)
The BBC article isn't saying that passwords are inherently bad, but that there are other methods that aren't as easy to implement badly.
The article itself though is slanted by getting its facts from a representative of a company that sells biometric identification technology (e.g. fingerprints).
Their company would benefit greatly from the elimination of text passwords.